Mitigate DoS Attack Using TCP Intercept On Cisco Router | PDF | Transmission Control Protocol | Denial Of Service Attack
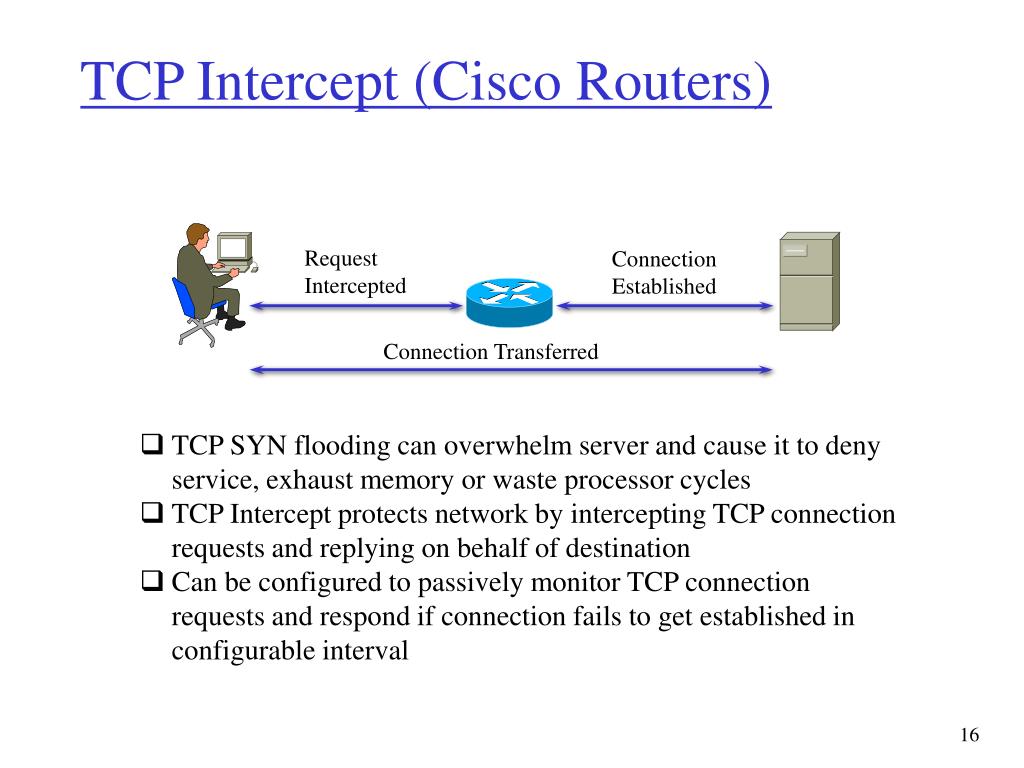
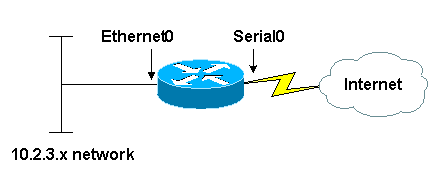
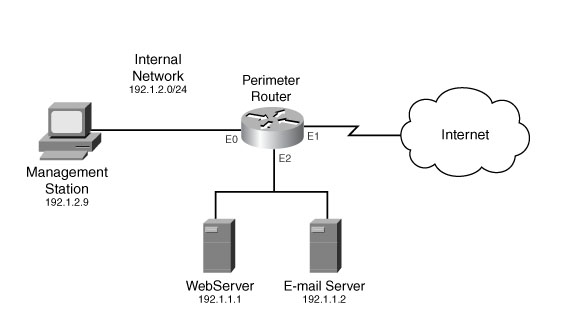
TCP Intercept :: Chapter 17. DoS Protection :: Part VII: Detecting and Preventing Attacks :: Router firewall security :: Networking :: eTutorials.org
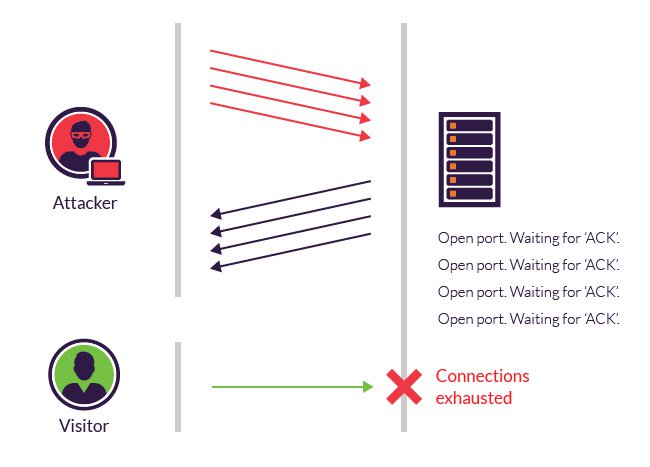
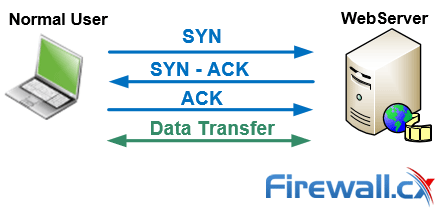
Best Practice - Protect Against TCP SYN Flooding Attacks with TCP Accept Policies | Barracuda Campus

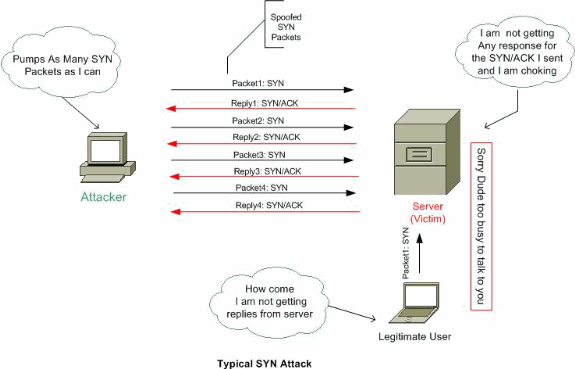
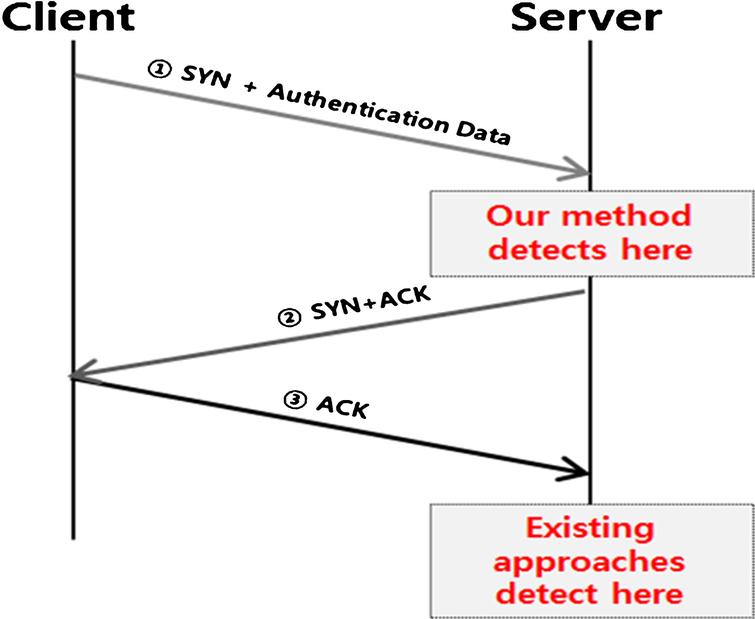
SYN flooding attack detection by TCP handshake anomalies - Bellaïche - 2012 - Security and Communication Networks - Wiley Online Library